Pam Gregory Free Birth Chart
Pam Gregory Free Birth Chart - Privileged access management (pam) is an identity security solution that helps protect organizations against cyberthreats by monitoring, detecting, and preventing unauthorized. Privileged access management (pam) identifies the people, processes, and technology that need privileged access and specifies policies to secure sensitive resources in an organization. Privileged access management (pam) is a security framework designed to protect organizations against cyberthreats by controlling and monitoring access to critical information. Privileged access management (pam) consists of the cybersecurity strategies and technologies for exerting control over the elevated (“privileged”) access and permissions for identities,. Privileged access management (pam) is a type of identity management and branch of cybersecurity that focuses on the control, monitoring, and protection of privileged accounts. Privileged access management (pam) is a comprehensive framework of policies, strategies, and technologies designed to regulate, oversee, and fortify access to critical. Pam is a cybersecurity strategy and set of technologies aimed at safeguarding an organization’s most sensitive data and critical systems by meticulously controlling and. Privileged access management helps organizations manage and secure access to their most critical systems, applications, and data, which are typically reserved for privileged accounts. Attorney general pam bondi has fired one of the top officials tasked with advising her and other senior doj officials of their ethical obligations, a source confirms. Privileged access management (pam) is a security framework designed to protect organizations against cyberthreats by controlling and monitoring access to critical information. Attorney general pam bondi has fired one of the top officials tasked with advising her and other senior doj officials of their ethical obligations, a source confirms. Privileged access management helps organizations manage and secure access to their most critical systems, applications, and data, which are typically reserved for privileged accounts. Privileged access management (pam) consists of the cybersecurity strategies and technologies for exerting control over the elevated (“privileged”) access and permissions for identities,. Privileged access management (pam) is a comprehensive framework of policies, strategies, and technologies designed to regulate, oversee, and fortify access to critical. Privileged access management (pam) is an identity security solution that helps protect organizations against cyberthreats by monitoring, detecting, and preventing unauthorized. Pam is a cybersecurity strategy and set of technologies aimed at safeguarding an organization’s most sensitive data and critical systems by meticulously controlling and. Privileged access management (pam) identifies the people, processes, and technology that need privileged access and specifies policies to secure sensitive resources in an organization. Privileged access management (pam) is a type of identity management and branch of cybersecurity that focuses on the control, monitoring, and protection of privileged accounts. Attorney general pam bondi has fired one of the top officials tasked with advising her and other senior doj officials of their ethical obligations, a source confirms. Privileged access management (pam) is an identity security solution that helps protect organizations against cyberthreats by monitoring, detecting, and preventing unauthorized. Privileged access management (pam) is a comprehensive framework of policies, strategies, and. Privileged access management (pam) consists of the cybersecurity strategies and technologies for exerting control over the elevated (“privileged”) access and permissions for identities,. Privileged access management (pam) is a type of identity management and branch of cybersecurity that focuses on the control, monitoring, and protection of privileged accounts. Privileged access management (pam) is a security framework designed to protect organizations. Privileged access management (pam) is a type of identity management and branch of cybersecurity that focuses on the control, monitoring, and protection of privileged accounts. Privileged access management (pam) is a comprehensive framework of policies, strategies, and technologies designed to regulate, oversee, and fortify access to critical. Privileged access management (pam) identifies the people, processes, and technology that need privileged. Privileged access management (pam) consists of the cybersecurity strategies and technologies for exerting control over the elevated (“privileged”) access and permissions for identities,. Privileged access management helps organizations manage and secure access to their most critical systems, applications, and data, which are typically reserved for privileged accounts. Privileged access management (pam) is a comprehensive framework of policies, strategies, and technologies. Privileged access management helps organizations manage and secure access to their most critical systems, applications, and data, which are typically reserved for privileged accounts. Privileged access management (pam) identifies the people, processes, and technology that need privileged access and specifies policies to secure sensitive resources in an organization. Privileged access management (pam) is an identity security solution that helps protect. Attorney general pam bondi has fired one of the top officials tasked with advising her and other senior doj officials of their ethical obligations, a source confirms. Privileged access management (pam) is a security framework designed to protect organizations against cyberthreats by controlling and monitoring access to critical information. Privileged access management (pam) consists of the cybersecurity strategies and technologies. Pam is a cybersecurity strategy and set of technologies aimed at safeguarding an organization’s most sensitive data and critical systems by meticulously controlling and. Privileged access management (pam) consists of the cybersecurity strategies and technologies for exerting control over the elevated (“privileged”) access and permissions for identities,. Privileged access management (pam) is a type of identity management and branch of. Pam is a cybersecurity strategy and set of technologies aimed at safeguarding an organization’s most sensitive data and critical systems by meticulously controlling and. Privileged access management helps organizations manage and secure access to their most critical systems, applications, and data, which are typically reserved for privileged accounts. Privileged access management (pam) is a type of identity management and branch. Privileged access management (pam) is a security framework designed to protect organizations against cyberthreats by controlling and monitoring access to critical information. Privileged access management (pam) is an identity security solution that helps protect organizations against cyberthreats by monitoring, detecting, and preventing unauthorized. Privileged access management helps organizations manage and secure access to their most critical systems, applications, and data,. Privileged access management (pam) consists of the cybersecurity strategies and technologies for exerting control over the elevated (“privileged”) access and permissions for identities,. Privileged access management (pam) is an identity security solution that helps protect organizations against cyberthreats by monitoring, detecting, and preventing unauthorized. Privileged access management (pam) is a type of identity management and branch of cybersecurity that focuses. Pam is a cybersecurity strategy and set of technologies aimed at safeguarding an organization’s most sensitive data and critical systems by meticulously controlling and. Privileged access management (pam) is an identity security solution that helps protect organizations against cyberthreats by monitoring, detecting, and preventing unauthorized. Privileged access management helps organizations manage and secure access to their most critical systems, applications, and data, which are typically reserved for privileged accounts. Privileged access management (pam) is a security framework designed to protect organizations against cyberthreats by controlling and monitoring access to critical information. Privileged access management (pam) consists of the cybersecurity strategies and technologies for exerting control over the elevated (“privileged”) access and permissions for identities,. Privileged access management (pam) is a comprehensive framework of policies, strategies, and technologies designed to regulate, oversee, and fortify access to critical. Attorney general pam bondi has fired one of the top officials tasked with advising her and other senior doj officials of their ethical obligations, a source confirms.Printable Birth Chart
Pam Gregory Everything That Happens in Our Life is Already in Our Birth Chart
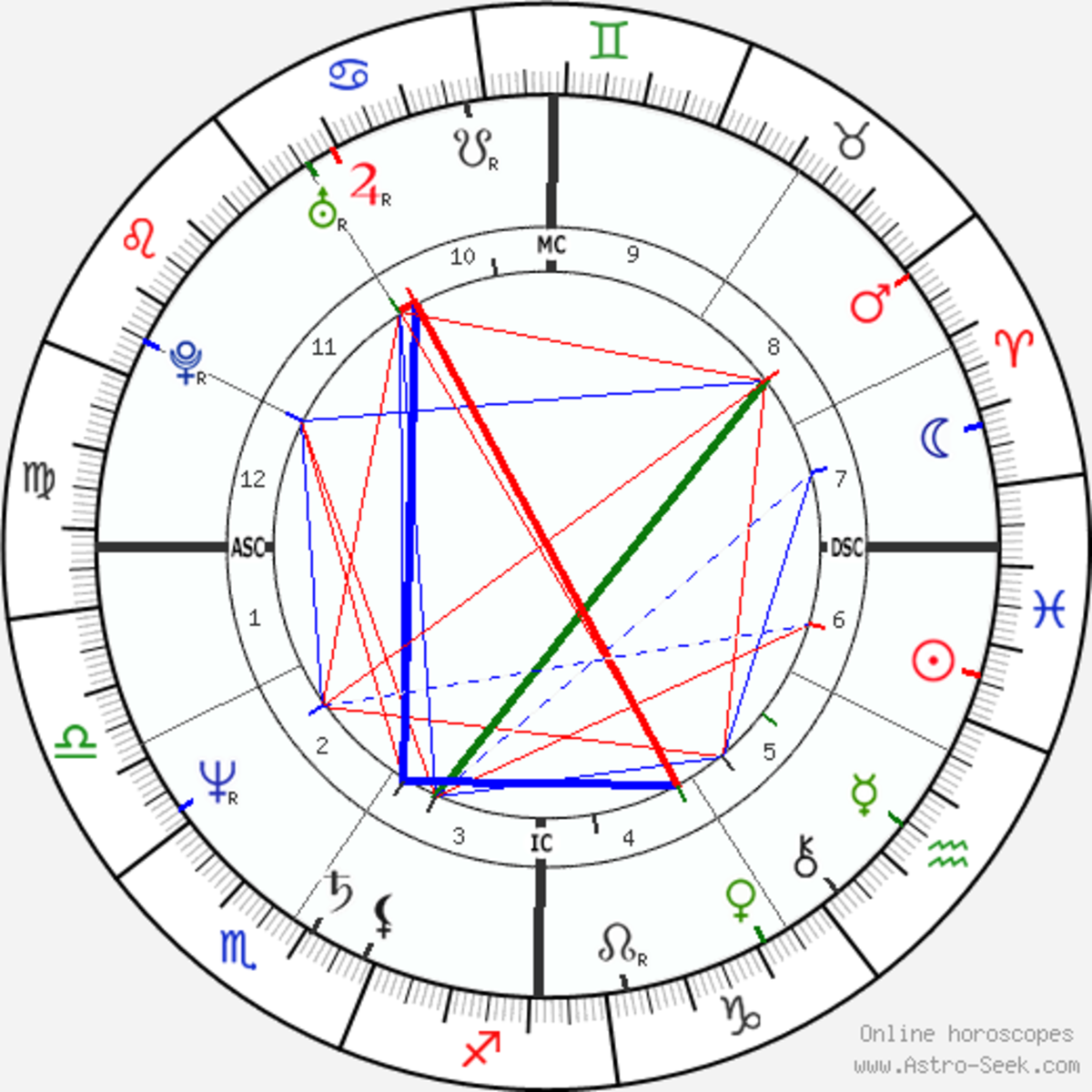
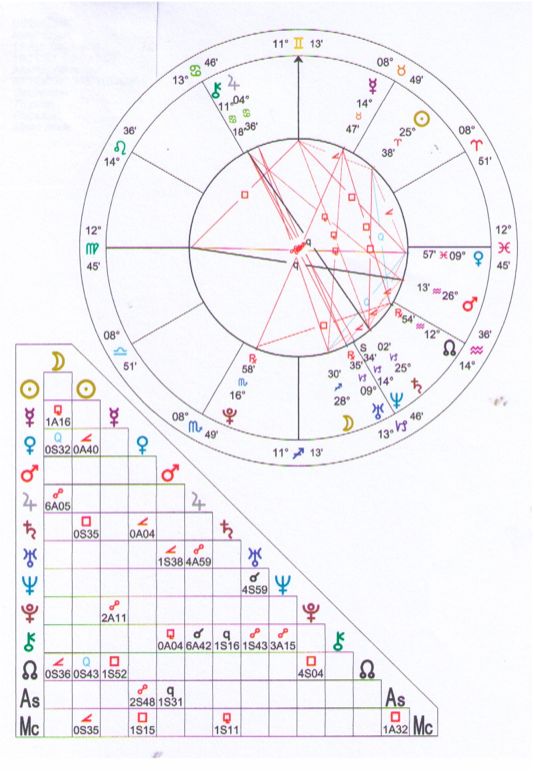
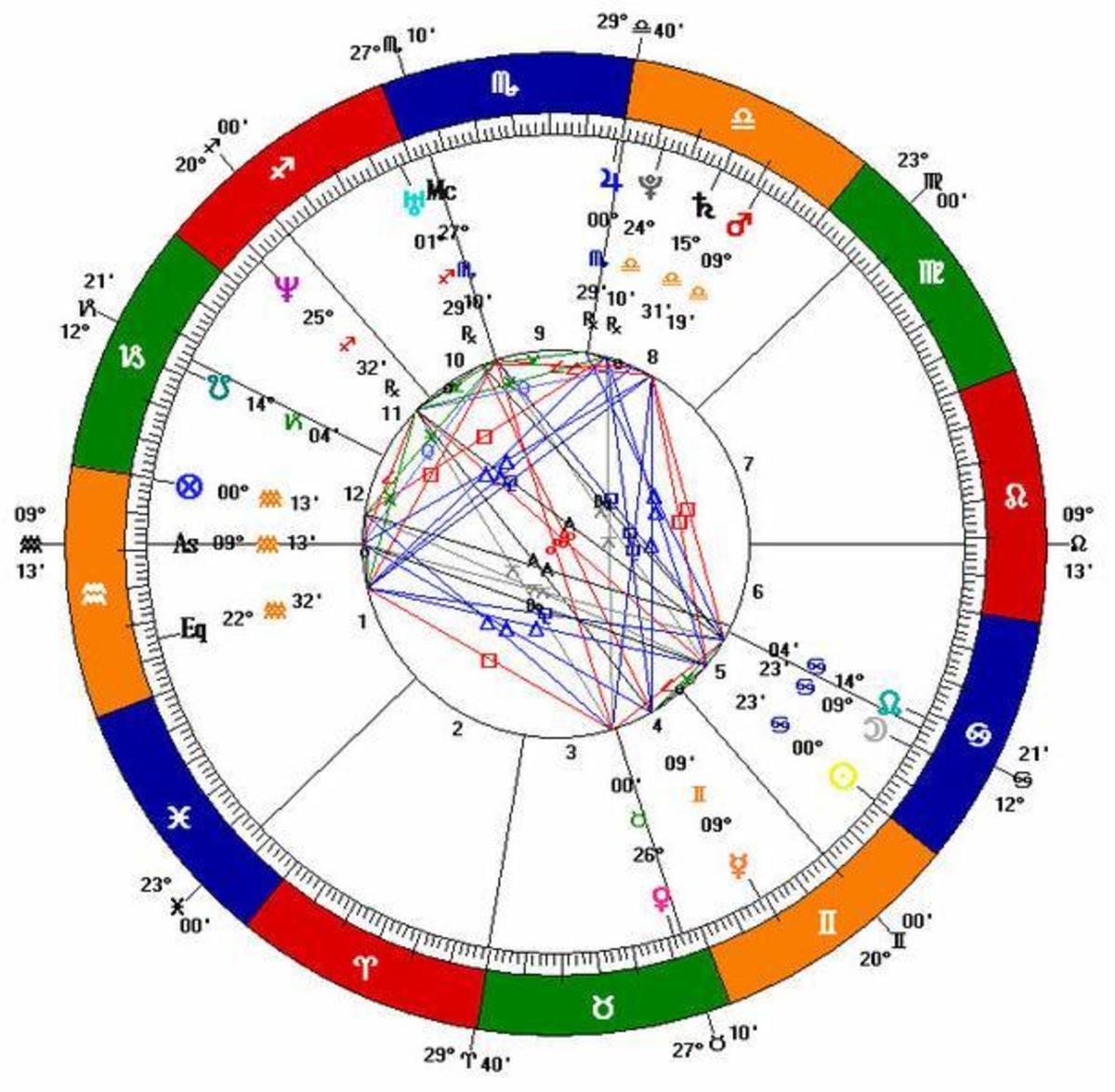
Astrology Birth Chart
Pin on 20+ Page Personalised Astrology (Birth) Chart
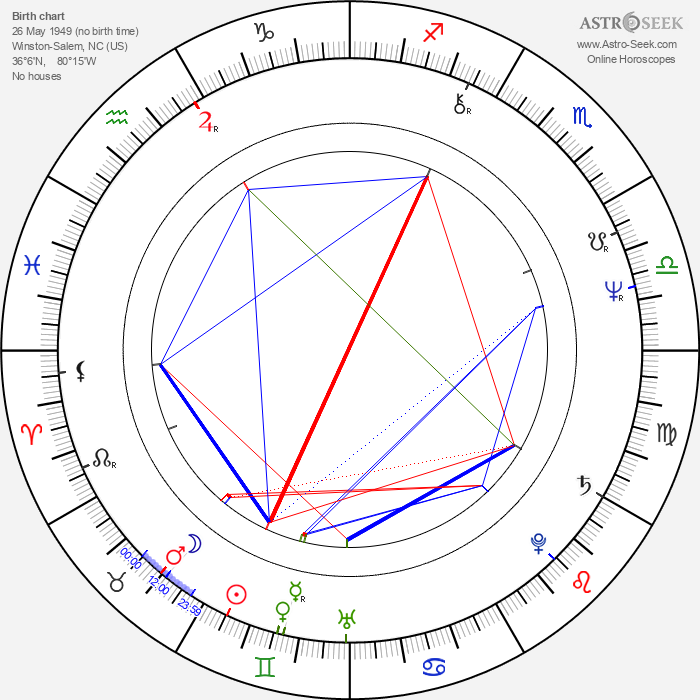
Birth chart of Pam Grier Astrology horoscope
Products and tutorial video series by Pam Gregory
my free birth chart analysis Chart birth horoscope daily astrology natal astrological
What Does an Ascendant or Rising Sign Mean in Your Birth Chart? HubPages
Get a detailed astrological analysis with this FREE instant interactive birth chart. No signup
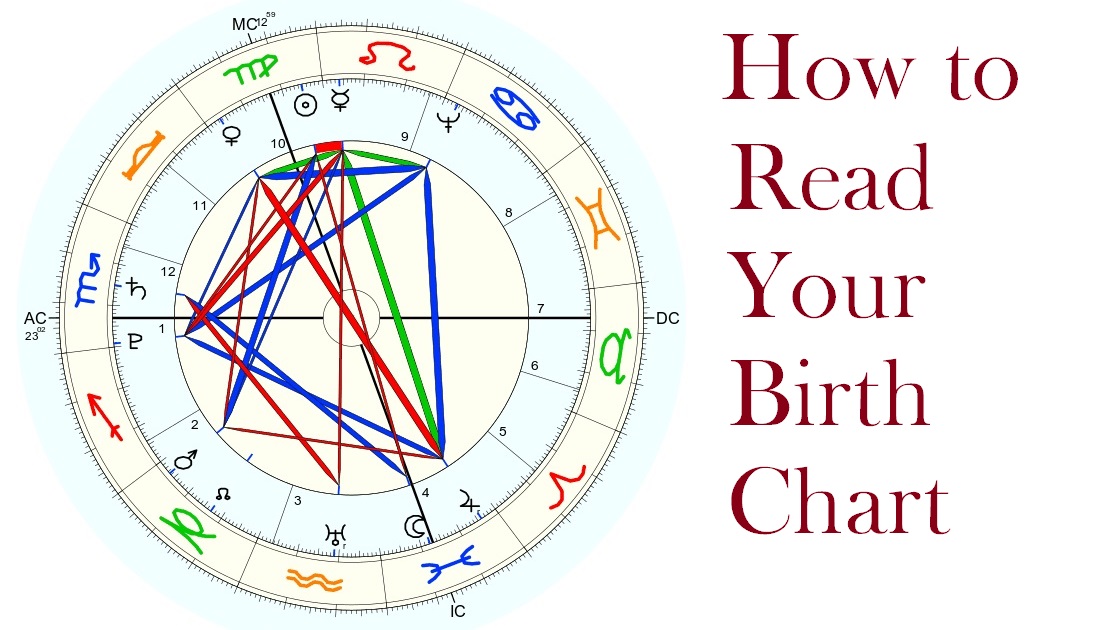
How to Read a Birth Chart The Beginner's Guide to Astrology
Privileged Access Management (Pam) Identifies The People, Processes, And Technology That Need Privileged Access And Specifies Policies To Secure Sensitive Resources In An Organization.
Privileged Access Management (Pam) Is A Type Of Identity Management And Branch Of Cybersecurity That Focuses On The Control, Monitoring, And Protection Of Privileged Accounts.
Related Post: